The enterprise perimeter is no longer fixed. It now shifts with each device, each user login, and each remote worksite. Enterprises must now consider home networks, branch offices, coworking spaces, and cloud environments to contribute to their growing number of endpoint interactions and, hence, endpoints, to increase their use of endpoint security and endpoint management solutions as part of their desktop management strategy.
At this point, enterprises have several hundred to thousands of endpoints. While the operational responsibility for these endpoints has been established, the endpoints have also become a safety and compliance liability.
In this blog post, we will understand what is endpoint security, how it relates to modern desktop management, core components of endpoint security, enterprise benefits of having a consolidated approach to managing endpoints, how it is different from traditional antivirus products, real-world scenarios where endpoint security has improved productivity for employees, and best practice examples of mature endpoint security solutions.
The procedure of safeguarding all devices that link up to an organization’s systems or utilize its data is termed endpoint security.
Examples of endpoints are: laptops, tablets, smartphones, virtual desktop environments, or any other gadget that connects to the internet and is used in conjunction with a business’s infrastructure or a company’s data. Devices are protected through the use of endpoint security software and appliance technologies that operate at the device level.
Endpoint protection is different from network security because the endpoint security solution monitors what is happening within a single instance of an end-user’s device. This includes what programs are running, processes running, and the person’s behavioral patterns.
Every unsecured endpoint increases exposure. With returned breach recovery costs of many millions of dollars, endpoint security has become a key component of a risk management strategy, rather than merely an IT operational requirement.
Desktop management is the operational control of all end-user devices, generally through centralization, including acquisition or provisioning, configuration, device lifecycle management, and eventual retirement of devices.
Today’s modern computing environment extends to the cloud, hybrid, and across a distributed architecture. Without centralized management of an organization’s end-user devices, i.e., workstations and mobile computing devices, scalability and greater management of enterprise IT become increasingly difficult. Modern Desktop Management solutions provide organizations with both scalability and increased operational control over their IT resources.
There is a direct relationship between endpoint management and endpoint security.
The combination of both yields a unified desktop management control environment and promotes compliance, return on investment, and operational efficiency through the effective use of resources deployed.
A complete endpoint security solution will include many interrelated layers working together:
These components work together to create robust and adaptive endpoint security solutions.
When it comes down to it, a mature endpoint security solution is made up of very robust capabilities that are executed in a disciplined manner. The individual tools do not define an endpoint security solution; rather, the way in which all the tools function together in a consistent framework identifies an endpoint security solution.
Core components of a mature endpoint security solution are:
To fully operate these capabilities, organizations should create a structured approach that includes the following:
Taken together, the above core components and operational practices provide a consistent and scalable framework for managing modern desktops in a secure, efficient, and effective manner.
Antivirus programs can still assist in the detection of malicious programs that have been created and released into the wild. Because the detection of malware relies on signature files, this form of protection will work best when used under controlled circumstances. The cyber threat environment continues to evolve, however, and there are now many attack methods that do not fit into the expected pattern of an attack.
Advancing attacks, such as fileless malware attacks, living off the land (LotL) attacks, and supply chain compromise, also do not leave behind any evidence of their presence. The failure of a company to properly protect its network and end-users can be attributed to the fact that it relied solely on traditional antivirus software and the detection of malware.
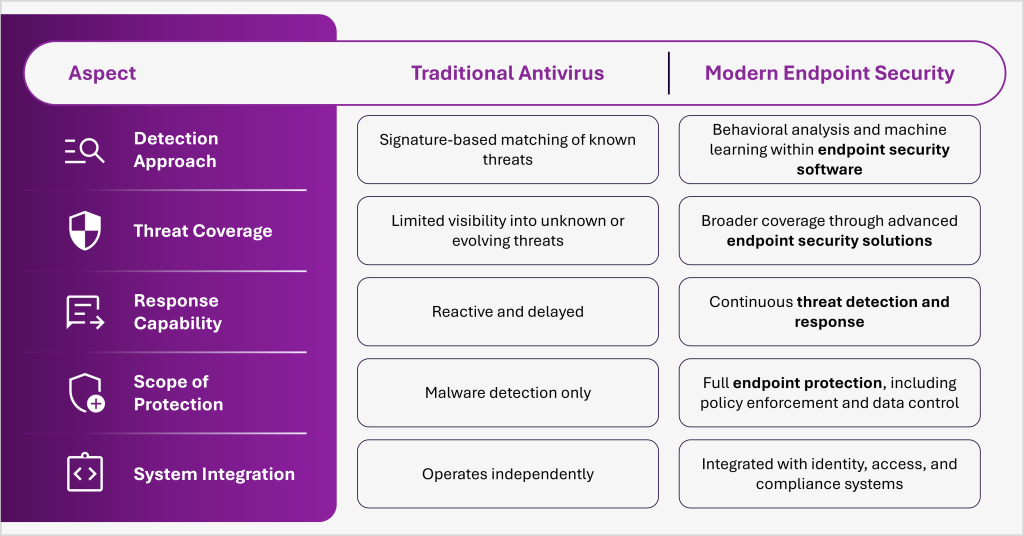
The move away from using only traditional antivirus software is due to both practical and theoretical reasons. Many large companies continue to use antivirus software not because it has become obsolete, but because it is inadequate for meeting all of their security needs.
An organization should have a clear understanding of what defines endpoint security today by using a model that incorporates visibility, control, and the ability to respond rapidly and effectively. For organizations handling sensitive information, relying solely on traditional antivirus software poses a serious operational risk.
Modern endpoint security solutions bridge the gap between detection and enforcement, and continually provide protection.
The importance of endpoint management and endpoint security is indicated by the different industries in which they are applied:
In addition to providing a consistent approach across all verticals, desktop management provides a uniform management approach for protecting endpoints through endpoint security solutions.
A global manufacturer was able to use Anunta’s MES Integrated Desktop environment to secure engineering and production endpoints on a large scale. The company implemented advanced threat detection and response capabilities within each virtual desktop and was able to monitor for anomalies in real-time across the plant’s entire system. This new proactive approach has greatly improved data breach prevention by protecting intellectual property, reducing downtime, and allowing for seamless, compliant access to remote staff in key production environments.
Endpoint security and desktop management together define enterprise resilience.
Fragmented approaches increase risk, cost, and inefficiency. Integrated models deliver control, visibility, and scalability.
Anunta’s Managed Endpoint Services unify endpoint management, security enforcement, and proactive threat response into a single operational model.
Did You Know: Anunta has over 30,000 endpoints in various industries and achieves a 76% proactive resolution rate and 99.98% uptime with managed endpoint security services.
To explore this further, see case study on Managed Endpoint Services.
With SOC 2 certification and alignment to HIPAA and PCI DSS, enterprises gain secure, compliant, and high-performing environments.
The outcome is clear:
To take the next step, talk to an endpoint security expert.